Application access
Apply for access or replication support
A stewarded path into self-hosted AI infrastructure.
Access to the current live node is application-based because it runs on finite self-hosted hardware and is intentionally stewarded, not operated as a mass public service.
The larger goal is not to centralize users on one machine, but to help more individuals, small groups, and aligned initiatives run their own self-hosted systems over time.
If you are interested in using the current system, exploring a shared-node model, or having us help you deploy your own node on your own hardware, you can apply below.
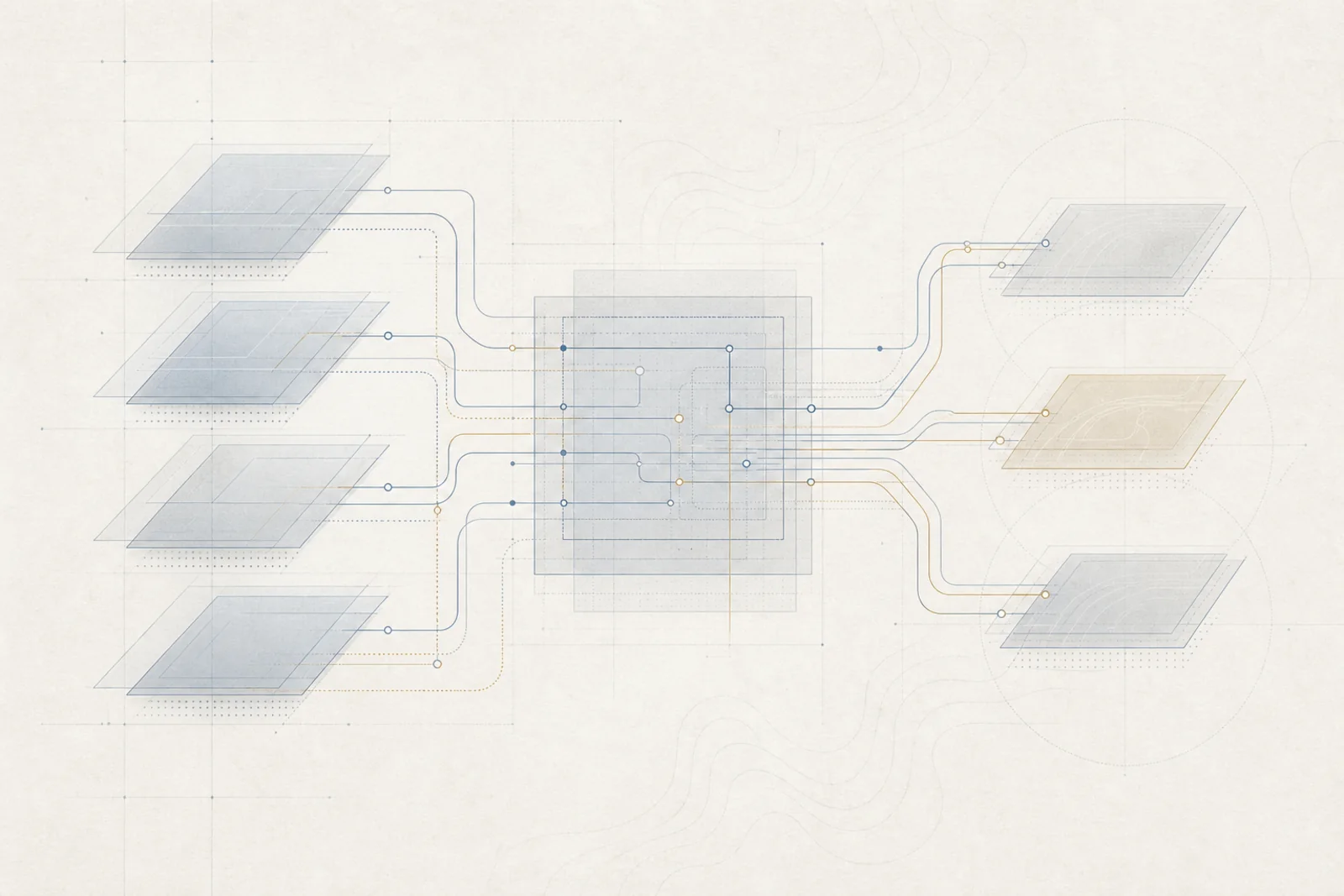
How it all connects
Why access is reviewed
The current node is powerful, but finite. It supports multiple workloads across conversation, operational tasks, coding, and other functions on one self-hosted machine. Access is therefore reviewed to protect reliability, preserve quality of service, and ensure the system is used in ways aligned with its purpose.
The goal is replication, not dependency
The long-term aim is not to turn one machine into a permanent central service for everyone. The aim is to help more individuals, small groups, and aligned organizations run systems of their own, so capability becomes more distributed, resilient, and independent.
A single well-configured machine in this class can often support one individual, a small trusted group, a small company, or a focused initiative, depending on the workload.
In many cases, the strongest model is a small group sharing one node, funding it together, and building local capability rather than depending on a distant platform.
Remote setup support
For aligned applicants who want their own setup, we may offer remote assistance in deploying a similar self-hosted node on user-owned hardware. This can help individuals, small groups, and organizations adopt a sovereign, private, and extensible AI environment without relying entirely on centralized platforms.
- User-owned hardware
- Remote setup assistance
- Self-hosted operation
- Practical deployment guidance
- A system that can serve one person or a small trusted group
Who this can help
- ◆Individuals who want a private personal assistant
- ◆Small groups of friends who want a shared self-hosted AI node
- ◆Creators who want publishing, production, and workflow support
- ◆Small companies that want an AI-assisted operations layer
- ◆Community initiatives that want local intelligence without platform dependence
- ◆Organizations exploring private alternatives to centralized tools
What it can be used for
Personal assistance
Memory, reminders, digests, context preservation, and reduced notification overload.
Small-team operations
Coding help, IT and infrastructure support, task routing, and operational assistance.
Client-facing business automation
Messaging bot intake, product understanding, follow-up questions, listing support, descriptions, metadata/SEO support, and publishing workflows.
Creative and production support
Repetitive technical preparation, output standardization, workflow assistance, and release support.
Federated communication and coordination
Room-based coordination, self-hosted communication, and user-controlled collaboration.
Selection is not pay-to-play
Voluntary support is never required to be considered, and the presence, absence, or size of a donation does not influence selection, priority, or approval.
Applications are reviewed based on alignment, seriousness, intended use, and fit with the mission.
Some projects may be supported without any donation at all. Others may be declined regardless of financial support if their goals are not aligned.
How applications are evaluated
This is a stewardship model, not a public utility and not a pay-for-access queue. We prioritize projects that increase human agency, reduce dependence on centralized systems, and help distribute capability rather than concentrate it.
We do not support projects centered on manipulation, surveillance, spam, exploitative automation, or uses that conflict with the public-interest purpose of the system.
Application intake
Keep submission email-only for now. You can copy the question template or open your email client with the template prefilled.
The same intelligence systems that can be used to concentrate power, capture attention, and shape behavior can also be used to distribute capability, protect attention, and return agency to the individual — if they remain transparent, replicable, and under the user's control.